The New Dirty War for Africa's uranium and mineral rights
Today, Friday 5 February at 08:30 CET, WikiLeaks releases a collection of documents that open up a corrupt multi-billion dollar war by Western and Chinese companies grab uranium and other mining rights in the Central African Republic (CAR) and escape paying for the environmental consequences. Among the hundreds of pages in this publication are detailed maps of mining rights, mining contracts with illegal kickbacks and secret investigative reports. The documents have been long sought by fraud investigators. In December 2015 a case was filed against Areva, alleging corruption related to the €1.8 billion purchase of three uranium mines in 2007.
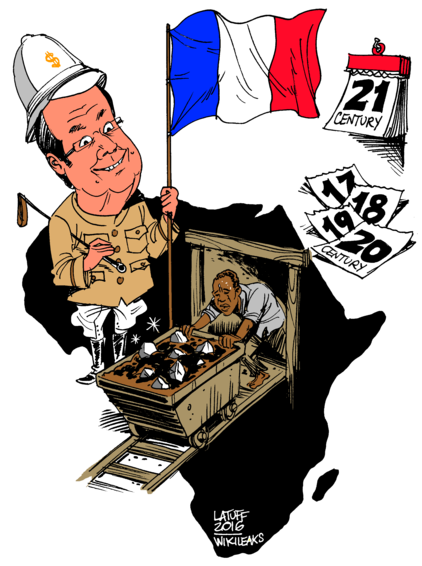
Effective oversight process by the local authorities is subverted either by duping state officials with deceiving front companies, such as the UN registered World Sports Alliance (WSA), now recycled into a cover for mining companies, or by corrupting them through the payment of 'cash bonuses'. After a profitable exploitation of resources, companies such as Areva – a French multinational group specialising in nuclear power – abandon the country, leaving behind nuclear contamination without having launched any of the promised investments.
- The mining sector in Central African Republic: an overall view
- AREVA and URAMIN scandal
- The World Sports Alliance (WSA): how the UN was indirectly implicated in a mining corruption scheme
- A state-company mining convention. What does it look like?
- PTI, or how the main Chinese state-owned defence company tried to enter into Central Africa
- Dig Oil in Central Africa: the adventures of a junior mining company
- Limestone, the unexploited resource of the Central African Republic
- Corruption and legal violations in the Central African Republic mining sector: international list of companies responsible
The mining sector in Central African Republic: an overall view
These documents provide a 360 degrees view on the mining sector and its relationships with one of the poorest countries in the world, Central African Republic, showing the numerous schemes put in place to avoid legal, impositive, social and environmental obligations by the mining companies and the growing difficulties of the states to implement their decisions.

View: HTML or PDF version.

View: HTML or PDF version.
AREVA and URAMIN scandal
The most powerful nuclear company in the world, AREVA, abandoned its Central African Republic exploitation without having launched any of the promised investments after an enormous political and financial scandal, amidst a social and environmental crisis, with skyrocketing radioactivity levels (up to 30 times the natural radioactivity in the zone) and literally transporting its former employees back to their homes like cattle. The following documents show the constant disdain of the company towards Central African Republic institutions and its population, and the neocolonial conditions of exploitation of its mines in Africa.
The World Sports Alliance (WSA): how the UN was indirectly implicated in a mining corruption scheme
These documents show the schemes used by a fake international organisation supported by the UN and numerous states in order to corrupt local elites and steal the natural resources of impoverished states and their populations.

View: HTML or PDF version.

View: HTML or PDF version.
A state-company mining convention. What does it look like?
A look into typical conventions between states and mining companies, the legal obligations arising from exploitation and research permits, the theoretical frame that limits the activities of non-state actors and the reality of their implementation, most often reduced to nothing.
PTI, or how the main Chinese state-owned defence company tried to enter into Central Africa
These documents show how the main Chinese state-owned defence company, specialising in missiles and tank production, tried to invest in Central Africa, probably within the framework of a hidden weapons agreement thought to feed the Central African Republic civil war in spite of global sanctions.

View: HTML or PDF version.
Dig Oil in Central Africa: the adventures of a junior mining company
These documents show the typical path of a junior mining company in an impoverished state in order to grab most of its resources as soon as possible and resell the permits immediately thereafter.

View: HTML or PDF version.
Limestone, the unexploited resource of the Central African Republic
These documents shed light on the incapacity of the Central African Republic government to exploit one of its lesser-known resources, limestone, the potential of which has been known for decades.
Corruption and legal violations in the Central African Republic mining sector: international list of companies responsible
This list shows in a very efficient way which companies intervene in the mining sector in CAR and how most of them violate their obligations toward the state, having corrupted its officials through "bonuses", paid most of the time in cash.

















































