Julian Assange calls for the appointment of a Special Prosecutor to investigate the NSA, after documents show US spying on WikiLeaks and its supporters.
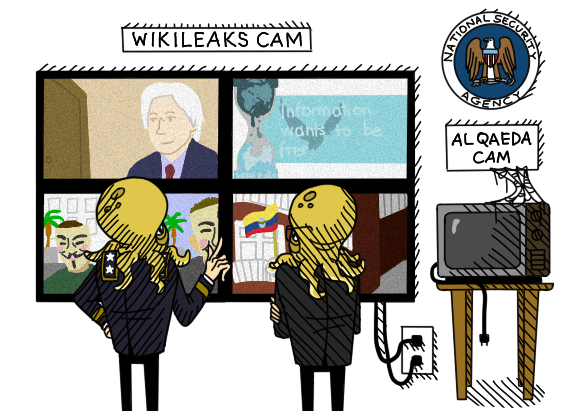
Today, documents were published from the national security whistleblower Edward Snowden, detailing US and UK spying efforts against the publishing organization WikiLeaks. One document shows that as far back as 2010 the US National Security Agency added WikiLeaks publisher Julian Assange to a “MANHUNTING” target list, together with suspected members of al-Qaeda. Another shows that the NSA wanted to designate WikiLeaks as a “malicious foreign actor” in order to expand the NSA's ability to target WikiLeaks staff, associates and supporters. And a third document, from 2012, demonstrates that the NSA's UK partner GCHQ also spied on WikiLeaks and its readers.
In response to these revelations WikiLeaks Editor Julian Assange has released the following statement:
'WikiLeaks strongly condemns the reckless and unlawful behavior of the National Security Agency. We call on the Obama administration to appoint a Special Prosecutor to investigate the extent of the NSA's criminal activity against the media including WikiLeaks and its extended network. News that the NSA planned these operations at the level of its Office of the General Counsel is especially troubling. No less concerning are revelations that the US government deployed "elements of state power" to pressure European nations into abusing their own legal systems; and that the British spy agency GCHQ is engaged in extensive hostile monitoring of a popular publisher's website and its readers. The NSA and its UK accomplices show no respect for the rule of law. But there is a cost to conducting illicit actions against a media organization. We have already filed criminal cases against the FBI and US military in multiple European jurisdictions. The FBI's paid informant, who attempted to sell information about me and my staff to the FBI, was imprisoned earlier this year. No entity, including the NSA, should be permitted to act against journalists with impunity. We have instructed our General Counsel Judge Baltasar Garzón to prepare the appropriate response. The investigations into attempts to interfere with the work of WikiLeaks will go wherever they need to go. Make no mistake: those responsible will be held to account and brought to justice.'
The disclosures come after yesterday's release of two new documents from the long-running US Grand Jury against WikiLeaks. As of November 2013 the United States Department of Justice has stated that the investigation continues.
For background on some of the US intelligence activities conducted against WikiLeaks, see Julian Assange's affidavit.