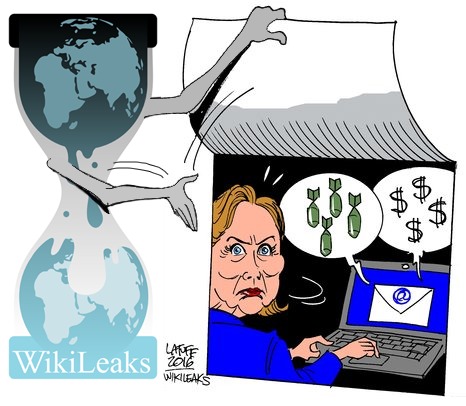
Hillary Clinton Email Archive
On March 16, 2016 WikiLeaks launched a searchable archive for over 30 thousand emails & email attachments sent to and from Hillary Clinton's private email server while she was Secretary of State. The 50,547 pages of documents span from 30 June 2010 to 12 August 2014. 7,570 of the documents were sent by Hillary Clinton. The emails were made available in the form of thousands of PDFs by the US State Department as a result of a Freedom of Information Act request. More PDFs were made available on February 29, 2016, and a set of additional 995 emails was imported up to February 2, 2018.
Common names for email recipients and senders courtesy of WSJ.